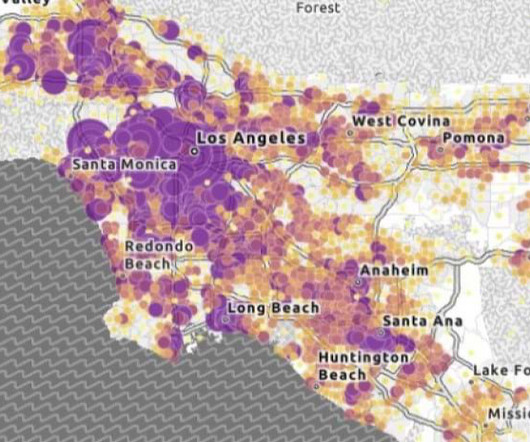
Designing and testing for accessibility in GIS and mapping
ArcGIS
MAY 13, 2024
Review best practices for designing and testing for accessibility maps and apps throughout the ArcGIS system during the development process.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.
ArcGIS
MAY 13, 2024
Review best practices for designing and testing for accessibility maps and apps throughout the ArcGIS system during the development process.

ArcGIS
MAY 13, 2024
Review best practices for designing and testing for accessibility maps and apps throughout the ArcGIS system during the development process.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
How to Optimize the Developer Experience for Monumental Impact
Generative AI Deep Dive: Advancing from Proof of Concept to Production
Understanding User Needs and Satisfying Them
Beyond the Basics of A/B Tests: Highly Innovative Experimentation Tactics You Need to Know
Leading the Development of Profitable and Sustainable Products
Knowledge Hut
APRIL 23, 2024
In cybersecurity, Remote Access Trojans (RATs) have become a major concern for individuals and businesses alike. These sneaky programs can infiltrate your system undetected, allowing hackers to take control of your computer remotely without you even knowing it. What is Remote Access Trojan (RAT)? So, what exactly is the RAT?
How to Optimize the Developer Experience for Monumental Impact
Generative AI Deep Dive: Advancing from Proof of Concept to Production
Understanding User Needs and Satisfying Them
Beyond the Basics of A/B Tests: Highly Innovative Experimentation Tactics You Need to Know
Leading the Development of Profitable and Sustainable Products

Snowflake
SEPTEMBER 27, 2023
From improving patient outcomes to increasing clinical efficiencies, better access to data is helping healthcare organizations deliver better patient care. But all of this important data is often siloed and inaccessible or in hard-to-process formats, such as DICOM imaging, clinical notes or genomic sequencing.

Advertisement
Think your customers will pay more for data visualizations in your application? Five years ago they may have. But today, dashboards and visualizations have become table stakes. Discover which features will differentiate your application and maximize the ROI of your embedded analytics. Brought to you by Logi Analytics.

Snowflake
OCTOBER 5, 2023
Learn how Europe’s leading embedded finance provider delivers data faster, decentralizes access and improves lineage controls with Snowflake’s Data Cloud. A cloud-first company finds simplicity with multiple providers Solaris is no stranger to using cloud solutions to drive efficient processes. That’s been really big for us,” he added.
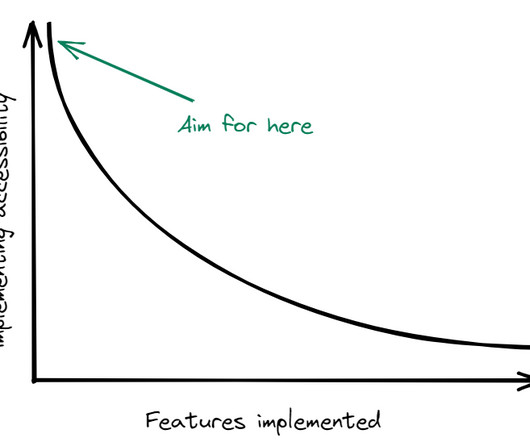
Scott Logic
NOVEMBER 6, 2023
Embedded Accessibility is a vision of building accessible products by default. We can consider accessibility embedded when it no longer needs to be prioritised because it is already at the core of the delivery process. Our products will also be more accessible by default. Does this sound familiar?
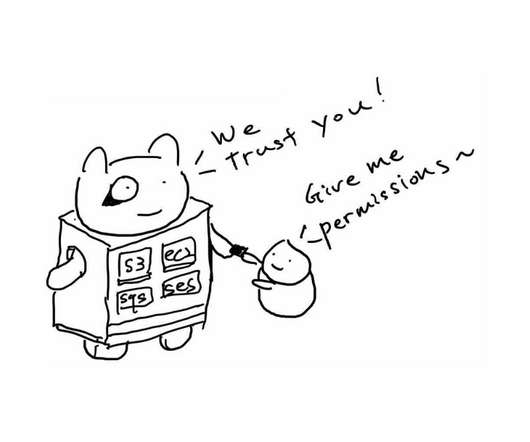
Netflix Tech
MARCH 10, 2021
ConsoleMe: A Central Control Plane for AWS Permissions and Access By Curtis Castrapel , Patrick Sanders , and Hee Won Kim At AWS re:Invent 2020, we open sourced two new tools for managing multi-account AWS permissions and access. Groups beyond software engineering teams are standing up their own systems and automation.

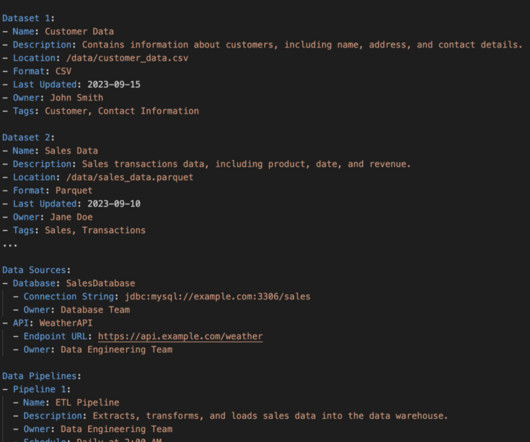
Precisely
APRIL 11, 2023
Let’s explore some of the questions you must ask as you begin the process, then dive into the solutions for common challenges you may face. Do I have access to the data? What do I need to do to access the data now and make it easy to find and access in the future? Where does that data live?
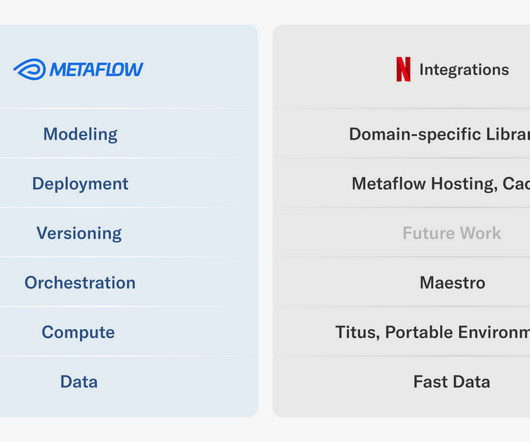
Netflix Tech
MARCH 7, 2024
The Machine Learning Platform (MLP) team at Netflix provides an entire ecosystem of tools around Metaflow , an open source machine learning infrastructure framework we started, to empower data scientists and machine learning practitioners to build and manage a variety of ML systems.

Snowflake
FEBRUARY 16, 2023
But it’s really hard and becoming increasingly harder to find and extract that data in a way that machines can process later,” explained Or Lenchner, CEO of Bright Data. But delivering so much data at speed isn’t easy, especially when you process trillions of requests a year for over 15,000 global customers.
Knowledge Hut
JANUARY 3, 2024
A system call is a function that a user program uses to ask the operating system for a particular service. User programmers can communicate with the operating system to request its services using the interface that is created by a system call. System calls serve as the interface between an operating system and a process.
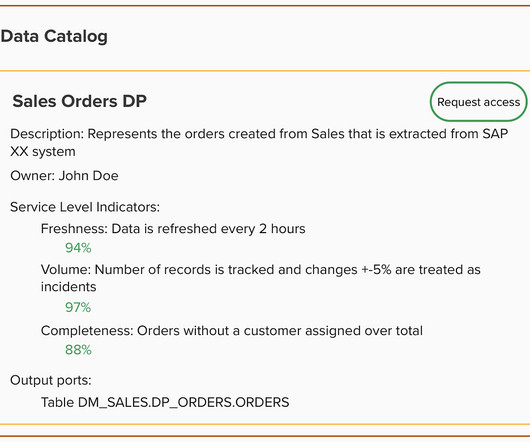
Towards Data Science
FEBRUARY 6, 2024
ERP and CRM systems are designed and built to fulfil a broad range of business processes and functions. The disconnection between the operational teams immersed in the day-to-day functions and those extracting business value from data generated in the operational processes still remains a significant friction point.
Knowledge Hut
JANUARY 28, 2024
The change control process is a crucial aspect of project management intended to manage and regulate changes made to the project plan, schedule, and budget. These change control process steps are planning, analyzing, approval, testing, implementing, and closing. The change request kickstarts the process of change control.

Precisely
SEPTEMBER 25, 2023
An important part of this journey is the data validation and enrichment process. Defining Data Validation and Enrichment Processes Before we explore the benefits of data validation and enrichment and how these processes support the data you need for powerful decision-making, let’s define each term. Let’s explore.

Knowledge Hut
MARCH 22, 2024
We may also deal with a lot of legacy systems with little documentation at work. Reverse engineering software is the process of dissecting it to understand its components, functionality, and workflow without having access to the source code. Legacy System Modernization. What is Reverse Engineering in Software Engineering?

Knowledge Hut
JANUARY 30, 2024
ITIL Processes ITIL comprises several processes that make it extremely adaptable, scalable, and diverse. These processes consist of activities with specified inputs, causes, and outputs. Let's look at some of the ITIL Processes and ideas that underpin them. This process is completed through five successive activities.

U-Next
FEBRUARY 16, 2023
As my thoughts started wandering around our Banking systems and Cosmos Bank Cyber-attack 2018. There is a rapid increase in banking frauds like identity theft, phishing, vishing, smishing, access to debit/credit card details, and UPI/QR code scams. The system should time and again monitor and report audit authorities.
Knowledge Hut
APRIL 25, 2024
Intrusion detection systems (IDS) are designed to identify suspicious and malicious activity through network traffic. So, let's get to know the meaning of an intrusion detection system and how it works. What Is a n Intrusion Detection System? Why Are Intrusion Detection Systems Important? and how it works.

Data Engineering Podcast
FEBRUARY 20, 2022
He also explains how he has architected the systems that ingest, process, and distribute the data that he is responsible for and the requirements that are introduced when collaborating with researchers, domain experts, and machine learning developers. What are some of the ways that you make your data accessible to AI/ML engineers?

Knowledge Hut
DECEMBER 27, 2023
System administrators are experts who manage several tasks and are appropriately referred to as "jacks of all crafts." System administrator abilities are useful in this situation. Recent automation and cloud computing advancements have created new opportunities for system administrators to pursue lucrative careers.
Edureka
APRIL 24, 2024
CISSP endorsement process refers to the final seal of approval, which only an approved ISC2-certified professional can grant after assessing your candidature. Table of Contents The CISSP ISC2 Endorsement Process – How To Get It? The CISSP ISC2 Endorsement Process – How To Get It? How do I get my CISSP endorsement?

Cloudera
JUNE 2, 2022
allowing developers to connect to any data source anywhere with any structure, process it, and deliver to any destination. How to onboard data into their system? I don’t care about their system. I want integration between all my systems. Each system is just one of many that I’m using.

Knowledge Hut
MARCH 13, 2024
If you aspire to be a software engineer, you must follow a specific strategy and understand the Google software engineer interview process to land your dream job. While Google’s hiring process is similar to other companies, it requires careful consideration. Triage different system issues and resolve them by analyzing their source.

U-Next
NOVEMBER 21, 2022
The HR functions and processes have been evolving with advances in technology, changing consumer behavior patterns, and increasing globalization of markets. It is the process of converting information into a digital format. It is utilized in all human resource processes to increase efficiency and streamline operations. .

Towards Data Science
APRIL 3, 2023
Building a Mental Model for Engineers and Anyone in Between Stream Processing can be handled gently and with care, or wildly, and almost out of control! By processing a smaller set of data, more often , you effectively divide and conquer a data problem that may otherwise be cost and time prohibitive.
Knowledge Hut
JANUARY 31, 2024
Managing competing priorities, costs, risks, and responsibilities necessitates a clear process and cross-functional collaboration. Exploring the principles, processes, and importance of ITIL service design. Process and performance enhancements Improved service consistency and quality What is Service Design?
Knowledge Hut
JANUARY 31, 2024
As business systems get increasingly complex, information technology plays a critical role in ensuring the smooth day-to-day functioning of present-day systems. It sees a business as a system of multiple sets of related components and activities that enable value creation. What is the impact of systems or subsystems outage?
Knowledge Hut
DECEMBER 5, 2023
If you have a passion for information technology (IT) and dream of turning it into a fulfilling career, ponder the path of a systems engineer. Join us on a detailed exploration of who can pursue a career as a systems engineer and the steps to become one in the year 2024. Who is a System Engineer, and What Do They Do?
Knowledge Hut
JANUARY 30, 2024
IT service lifecycle processes and stages are covered in five books that have been revised several times over the years. All professionals who want to take the exam for the ITIL 4 Foundation Certification must have a thorough understanding of the ITIL 4 framework and ITIL processes list.
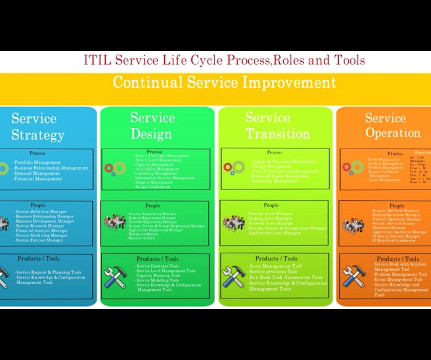
Knowledge Hut
JANUARY 29, 2024
It facilitates the practical framework for the authority of various procedures related to the IT processes. The tactical components comprise of individual processes that would monitor the assignments and activities required to execute the service. Here is the detailed description of each of these processes.

Knowledge Hut
JANUARY 30, 2024
So, this framework provides uniform and consistent guidelines to all IT industries to define their IT Service Management processes. John explained that companies, understanding the importance of consistent process, have embraced lessons from the industry and continually improvise their processes for better customer experience.
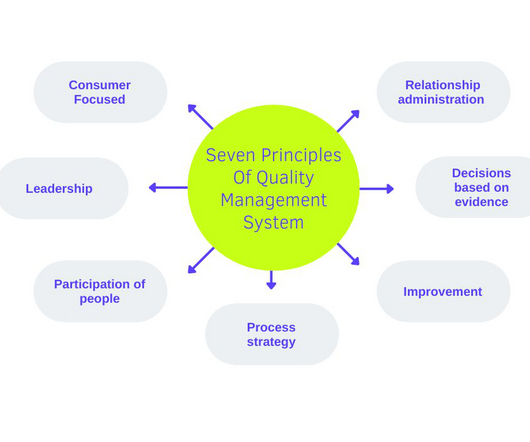
Edureka
FEBRUARY 20, 2023
Principles of Quality Management System: Quality planning, assurance, control, and improvement are the four primary parts of quality management. To hold them to a high and consistent level, quality management monitors the activities, tasks, and processes (inputs) utilised to produce a product or service (outputs).

LinkedIn Engineering
DECEMBER 16, 2022
She highlights for us the impactful work she found here �����from ushering in LinkedIn���s next-generation, server query system that runs over a fleet of 350,000 servers, to mentoring the next generation of female engineers: In my engineering career, I���ve always followed the path less taken.
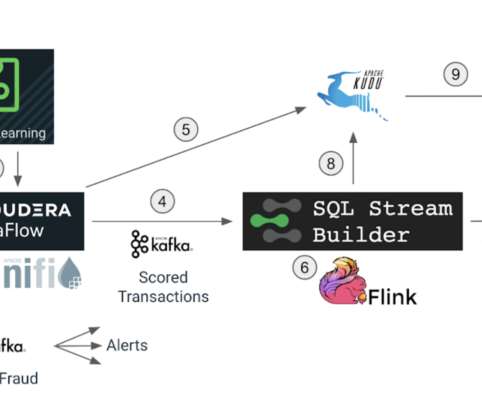
Cloudera
JULY 18, 2022
In this blog we will conclude the implementation of our fraud detection use case and understand how Cloudera Stream Processing makes it simple to create real-time stream processing pipelines that can achieve neck-breaking performance at scale. Flink is a “streaming first” modern distributed system for data processing.

Knowledge Hut
OCTOBER 4, 2023
Below are the Power BI requirements for the system. Supported operating system: Power BI program can be installed in a device with the following operations systems. Database SQL database Access database Oracle database IBM Netezza MySQL database Sybase database Power Platform Power BI dataset Dataflows 4.

Knowledge Hut
APRIL 29, 2024
The stakes are high in the banking and financial industry since substantial financial sums are at risk and the potential for significant economic upheaval if banks and other financial systems are compromised. One of the officials fell for the phishing email and clicked on a dubious link, which allowed the malware to hack the system.

Databand.ai
JULY 19, 2023
Complete Guide to Data Ingestion: Types, Process, and Best Practices Helen Soloveichik July 19, 2023 What Is Data Ingestion? Data Ingestion is the process of obtaining, importing, and processing data for later use or storage in a database. However, the ultimate goal is simple: to prepare data for immediate use.
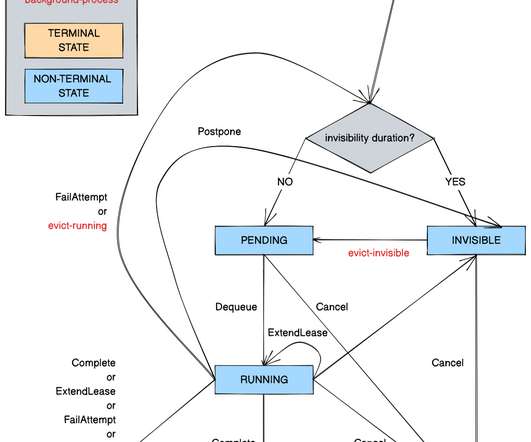
Netflix Tech
SEPTEMBER 29, 2022
Timestone: Netflix’s High-Throughput, Low-Latency Priority Queueing System with Built-in Support for Non-Parallelizable Workloads by Kostas Christidis Introduction Timestone is a high-throughput, low-latency priority queueing system we built in-house to support the needs of Cosmos , our media encoding platform. Over the past 2.5

Knowledge Hut
FEBRUARY 29, 2024
for creating an interactive service, especially with the external system; you must go through this article, If you are eager to learn more, then learn node js online. process exit situation. To explain the process methods, we are using the VS Code studio and its terminal. exit process. But if you are using Node.js
phData: Data Engineering
SEPTEMBER 19, 2023
However, to fully harness the potential of a data lake, effective data modeling methodologies and processes are crucial. With many data modeling methodologies and processes available, choosing the right approach can be daunting. Efficiency through being able to streamline data storage and retrieval processes.

Snowflake
APRIL 29, 2024
DORA: Building a More Secure Financial System DORA, enacted in January 2023, moves beyond reactive measures, requiring FEs and their service providers to proactively identify vulnerabilities, prevent disruptions and plan for swift recovery from incidents. Five Core Pillars of DORA 1.

Snowflake
SEPTEMBER 11, 2023
This wide adoption of legislation requires organizations that store or process personally identifiable information (PII) to have greater control over that data, and better transparency about how they store it. These highlighted sections are of particular importance because sections will be enforced as soon as September 22, 2023. 1, Section 3.2,
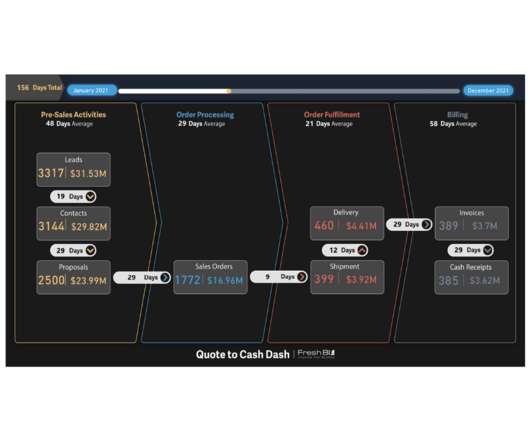
FreshBI
MAY 25, 2021
Business Processing Dashboards Explained A Business Workflow is visual representation of steps through a business activity used to support and validate your Business Intelligence Objectives. Overall Business Efficiency: Business Processing Dashboards are the epitome of heightened business efficiency.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content